An SSL certificate is an excellent starting point for any website, as it creates a secure path for user data. While encryption is vital for a modern platform, your setup also needs server-level defenses to fix internal vulnerabilities. Many users looking for the cheapest domain and hosting in India find that a basic server often lacks the active defense needed to catch a breach before it leads to extended downtime. Exploring Hostinger alternatives in India is often the first step toward finding an environment that prioritizes invisible, deep-layered protection over simple SSL requirements.
Relying on basic security measures is a risk that most growing businesses eventually face. As cybercriminals shift toward automated, rapid-fire attacks, your hosting must act as a dynamic shield, neutralizing threats at the network layer rather than waiting for a malware attack to appear in your core files. In 2026, the average time from a vulnerability being discovered to being exploited is under five days, meaning your defense must be instantaneous to be effective.
In This Blog, We Will Talk About…
(Jump to the section that interests you the most!)
Defining Website Security In 2026
Modern website security involves a comprehensive shield for your application, server environment, and visitor data. It is the practice of neutralizing unauthorized attempts to access or alter your digital property. In 2026, this means moving toward zero-trust architectures where every request is verified before it reaches your core files.
A truly secure environment utilizes behavioral analysis to distinguish between a genuine customer and a malicious script acting as a browser. These are some of the popular trends to look out for in 2026 –
This foundational protection ensures your business remains operational and your brand reputation stays intact.
Prevalent Website Security Threats
Modern botnets function as digital trackers, scanning millions of websites every hour to find a single unpatched script or a configuration oversight. Their goal isn’t always a quick data heist; they often hijack your server power to fuel larger attack networks or copy your original content. Even common threats like SQL injections have evolved to target specific API endpoints, bypassing your frontend to communicate directly with your database.
Without a system that monitors file integrity at the server level, these intruders can remain in your directories for months, quietly draining your traffic and your brand’s reputation.
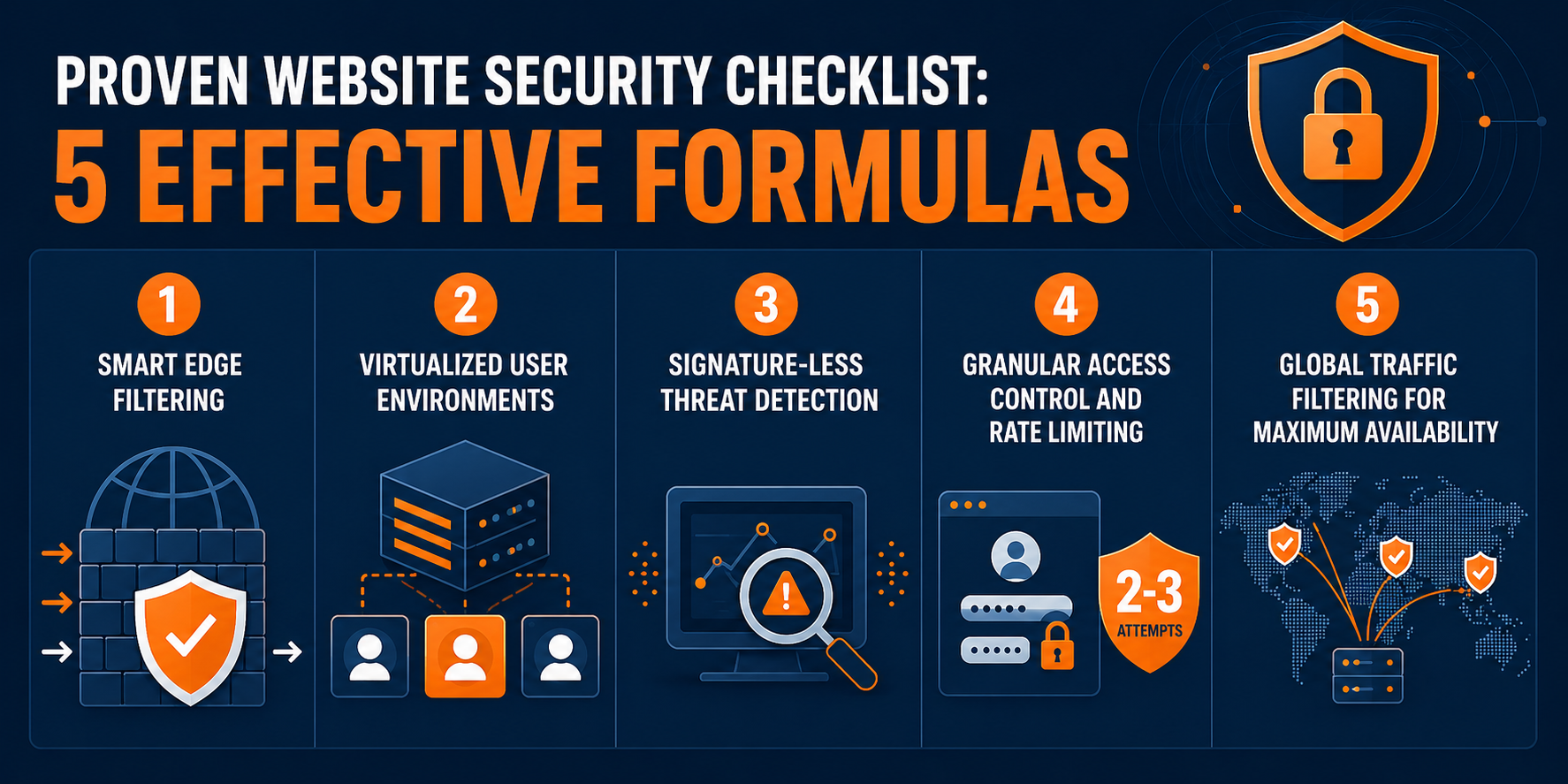
Proven Website Security Checklist: 5 Effective Formulas
1. Smart Edge Filtering
Traditional firewalls are too slow for today’s threats. You need a Web Application Firewall (WAF) that blocks malicious payloads at the network edge, long before they even touch your website’s local resources.
By evaluating the structure of every incoming packet, the system can drop malicious payloads associated with zero-day exploits. This ensures that your server resources are spent only on processing legitimate human traffic.
2. Virtualized User Environments
Many hosting environments fail because they allow weak boundaries between different websites on the same machine. Your hosting setup must use advanced virtualization to keep every account’s resources isolated. This ensures that even if a separate website on the network is breached, the intruder cannot move into your directory. This proactive threat detection helps you avoid the high costs of emergency data recovery and loss of customer trust.
3. Signature-Less Threat Detection
Because hackers are constantly rewriting their code to bypass standard antivirus filters, your hosting needs a system that tracks suspicious activity instead. This behavioral analysis looks for intent rather than just matching file names against a database. It allows your hosting to block brand-new threats that haven’t been documented by security researchers yet.
4. Granular Access Control and Rate Limiting
Control panels are the most frequent entry point for automated login attempts. To prevent unauthorized entry, your hosting infrastructure needs strict rate limiting that blocks an IP address after only two or three failed attempts. Implementing two-factor authentication at the server level provides a manual layer of verification that software alone cannot bypass. This ensures that even if an administrative password is compromised, your central control panel remains inaccessible to outside parties.
5. Global Traffic Filtering for Maximum Availability
During a massive traffic spike, local bandwidth will fail. Modern defense routes your traffic through global filtering centers and eliminates the malicious requests, ensuring that only legitimate traffic reaches your site. MilesWeb integrates this enterprise-grade defense, including free professional email accounts and daily backups, to ensure your business communications and data remain preserved regardless of external attacks.
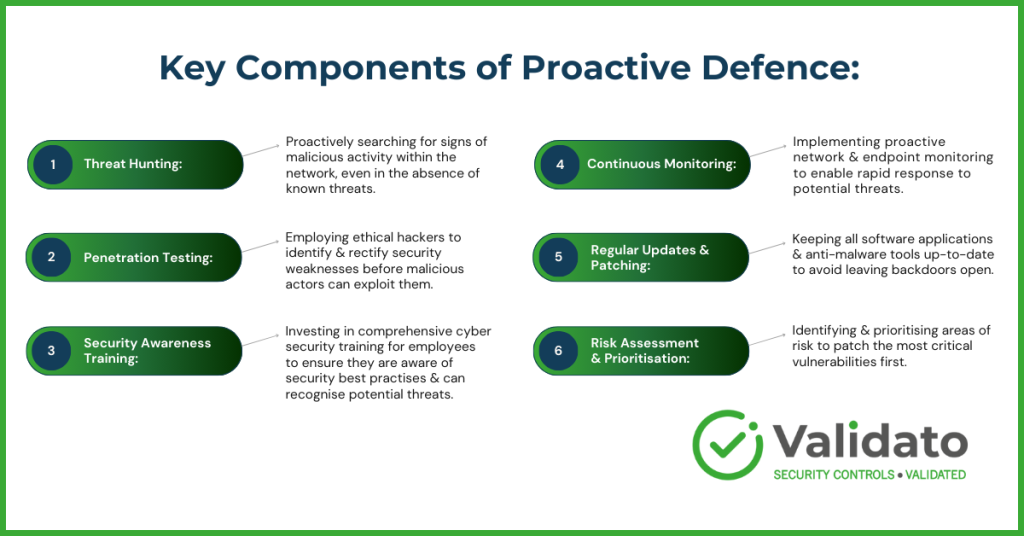
Strategic Importance Of Proactive Defense
Building a fortified infrastructure ends the pattern of responding to preventable technical issues. When your server handles the heavy lifting of threat detection, you avoid the high costs of emergency data recovery and the “Deceptive website ahead” warning in your customer’s browser. A clean security record is a performance booster, keeping your website fast and reliable by preventing background malicious processes from consuming your CPU.
Prioritizing security directly safeguards your earnings. The average cost of a data breach for a small business in 2026 is approximately $3.31 million, with 60% of small firms closing within six months of a major incident. By maintaining a clean, secure record, you ensure that every visitor sees your content without interruption, avoiding intrusive warnings or lag caused by background malicious processes.
Concluding Insights
Digital resilience involves a security architecture that moves past the standard SSL certificate. Encryption is a basic requirement, yet the true security of your platform relies on strict resource isolation and an advanced network firewall. Implementing isolated resources and automated threat response mechanisms creates a reliable environment for your visitors.
MilesWeb provides this level of infrastructure, offering professional email accounts and daily backups to maintain your professional identity. These five security strategies build a professional foundation for your website, allowing you to reach your ambitious goals.